Sony Part 2 [012]
Posted on Tuesday, Feb 24, 2026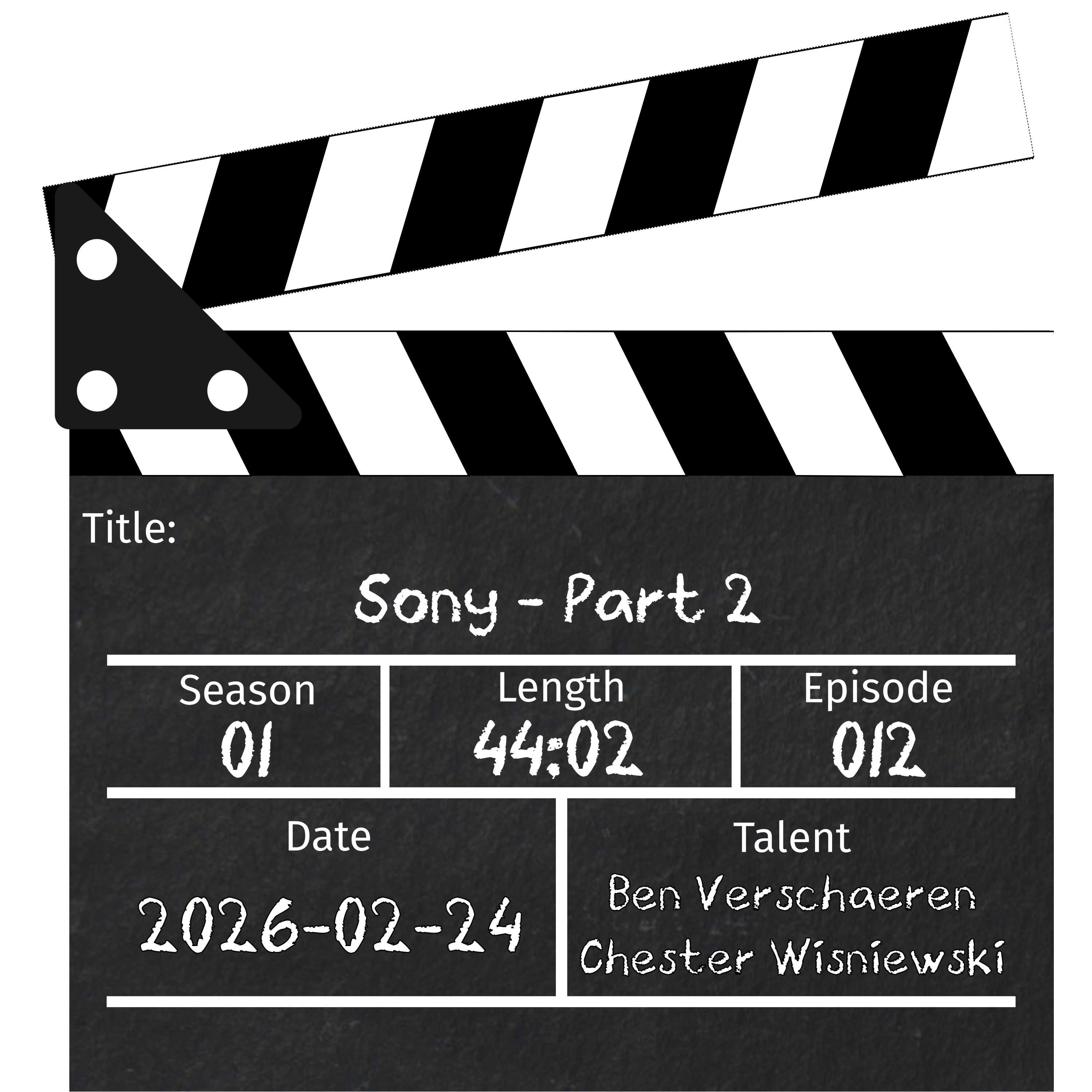
Show Notes
Our last episode covered Sony’s cybersecurity woes from 2005 until 2011, we pick up where we left of in the midst of the 50 days of LulzSec. This episode covers everything up until the alleged theft of the PS5 root signing keys in January 2026. So much s0wnage and so little time…
2014 Sony Pictures hack - Wikipedia
Lizard Squad - Wikipedia
Kim Dotcom May Have Just Saved Holiday Gaming - Gizmodo
Hackers Used Sophisticated SMB Worm Tool to Attack Sony - Security Week
Hacker group claims it breached Sony’s PlayStation Network and stole information - Business Insider
‘All Of Sony Systems’ Allegedly Hacked By New Ransomware Group - Kotaku
Ransomed.vc group claims hack on ‘all of Sony systems’ - CyberDaily.au
Sony Confirms Data Breach - Gamerant
Sony confirms data breach impacting thousands in the U.S. - Bleeping Computer
CTRL-ALT-CHAOS - Elliott & Thompson
PS5 ROM Keys Leak: What Happened, Why it Matters, and How it Impacts Security? - PC Quest
PS5 Open to Hacks and Jailbreak as ROM Keys Leak – Report - PlayStation Lifestyle
Sony Pictures Statement Related To Lulzsec Attack - Sony
Member Of LulzSec Hacking Group Sentenced To Over Year In Federal Prison For 2011 Intrusion Into Sony Pictures Computer Systems - Department of Justice
Sony Online President’s Flight Diverted After Hacker Bomb Threat - Kotaku
Update on Sony Investigation - FBI
TA14-353A: Targeted Destructive Malware - Seclists
PlayStation Network Update - Sony
American and Dutch Teenagers Arrested on Criminal Charges for Allegedly Operating International Cyber-Attack-For-Hire Websites- Department of Justice
PlayStation social media accounts briefly hacked - We Live Security
PlayStation Social Media Accounts Hacked - Security Week
Breach letter - Sony victim
#StopRansomware: CL0P Ransomware Gang Exploits CVE-2023-34362 MOVEit Vulnerability - CISA
Sony Confirms Data Stolen in Two Recent Hacker Attacks - Security Week
Hosts

Chester Wisniewski (He/Him)
Chester Wisniewski is an old hat to information security having practiced the art professionally for more than 25 years. Starting out with a 300 baud modem in the 80s he became obsessed with exploring the world’s phone networks (phreaking?) which inevitably led to bulletin boards and early internet access in the mid-80s. The trust inherent in the system seemed absurd and this inspired Chester to pursue how we might build systems less prone to abuse. The rest is history.

Ben Verschaeren (He/Him)
Ben has been in Information Technology for two decades starting at the age of 14. Recently described by a senior executive as an “Adult Dennis the Menace”, Ben’s always up for a bit of cyber mayhem. Having worked across, Managed Services Providers, two of Australia’s largest Enterprises and an almost decade at a Security Vendor. Ben’s experience spans Wintel System Administration, Network Administration, Penetration Testing, and Software Development.