WannaCry [010]
Posted on Tuesday, Aug 19, 2025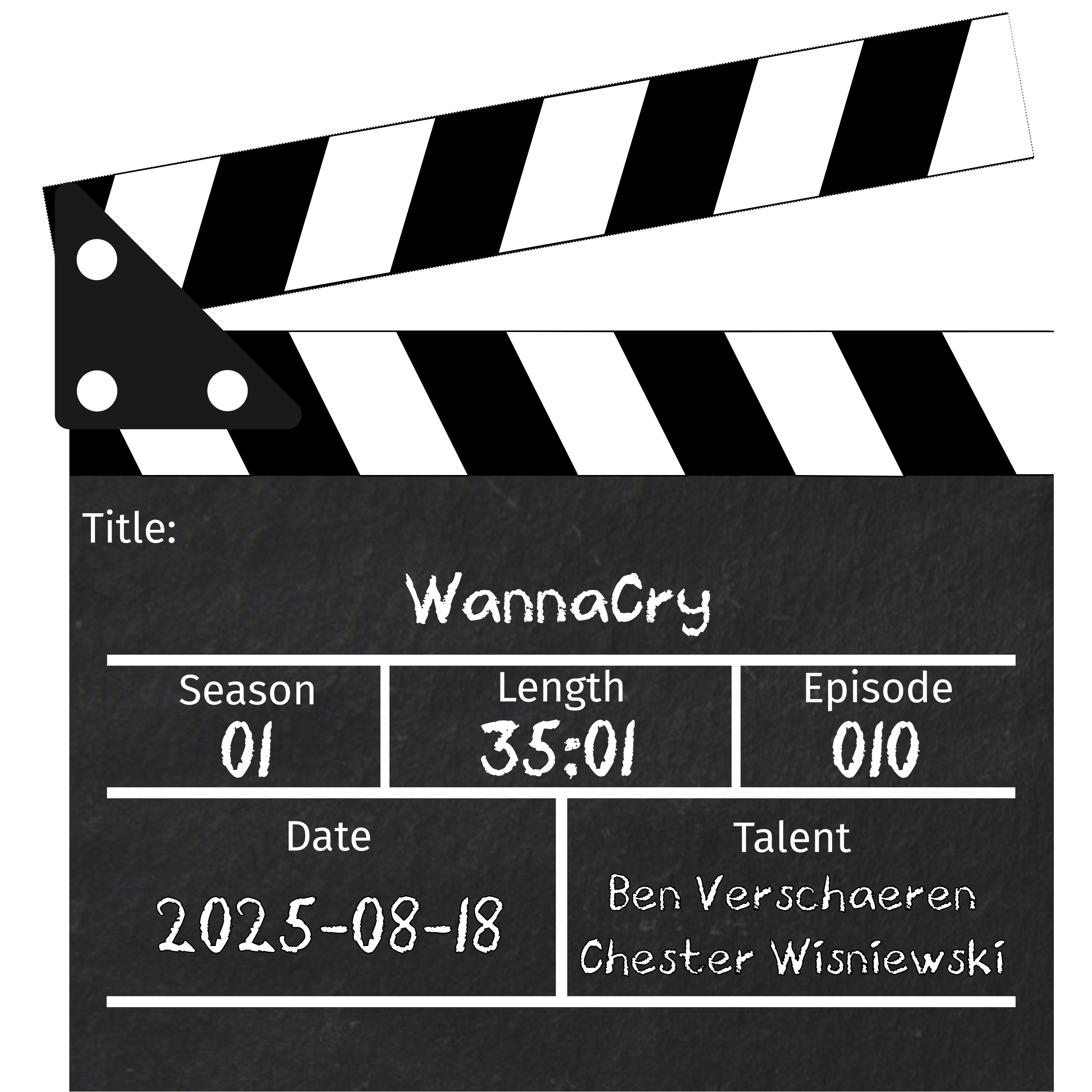
Show Notes
May 12, 2017 was memorable for many in the information security industry, but it was also memorable in health care, manufacturing, shipping and more as the WannaCry worm laid waste to unpatched Windows machines the world over. May it be the last widespread worm we need to cover on this podcast…
Wikipedia - WannaCry
Microsoft - MS17-010
The Hacker News - TSMC Chip Maker Blames WannaCry Malware for Production Halt
Arstechnica - NSA Leaking Shadow Brokers Just Dumped Its Most Damaging Release Yet
NCCIC - What is WannaCry/WanaCryptor
Arstechnica - An NSA Derived Ransomware Worm is Shutting Down Computers Worldwide
NIH - NHS ransomware attack spreads worldwide
Wired - Accidental Kill Switch Slowed Friday’s Massive Ransomware Attack
Zero Day - U.S. Government Disclosed 39 Zero-Day Vulnerabilities in 2023, Per First-Ever Report
Arstechnica - Wanna Decryptor Kill Switch Analysis
Sophos - WannaCry Aftershock
Microsoft - Customer Guidance For WannaCrypt Attacks
The Hacker News - WannaCry Ransomware Bitcoin
Gov.UK - Foreign Office Minister condemns North Korean actor for WannaCry attacks
White House - Press Briefing on the attribution of the WannaCry malware attack to North Korea\
Hosts

Chester Wisniewski (He/Him)
Chester Wisniewski is an old hat to information security having practiced the art professionally for more than 25 years. Starting out with a 300 baud modem in the 80s he became obsessed with exploring the world’s phone networks (phreaking?) which inevitably led to bulletin boards and early internet access in the mid-80s. The trust inherent in the system seemed absurd and this inspired Chester to pursue how we might build systems less prone to abuse. The rest is history.

Ben Verschaeren (He/Him)
Ben has been in Information Technology for two decades starting at the age of 14. Recently described by a senior executive as an “Adult Dennis the Menace”, Ben’s always up for a bit of cyber mayhem. Having worked across, Managed Services Providers, two of Australia’s largest Enterprises and an almost decade at a Security Vendor. Ben’s experience spans Wintel System Administration, Network Administration, Penetration Testing, and Software Development.